Cisco CCNP ROUTE Planning for EIGRP
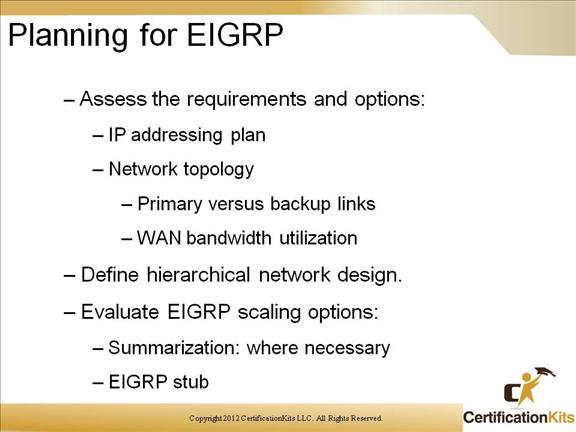
When implementing EIGRP (as well as other routing protocols) coming up with an IP Address plan that maps to a network topology is key. The IP Address plan should be implemented with IP Address summarization in mind which if implemented properly can decrease routing table sizes on routers while increasing efficiency.
Cisco CCNP ROUTE EIGRP Implementation Plan
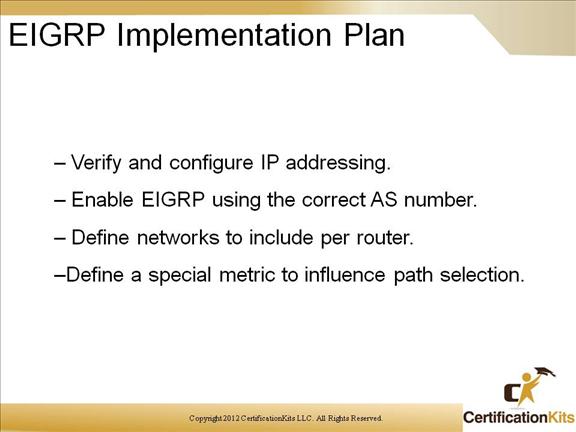
When implementing remember that unlike OSPF which uses a Process ID for the routing instance which can be different on each router, EIGRP uses an Autonomous System number which MUST be the same on all routers that will be exchanging routes via EIGRP. Networks must be defined under the respective EIGRP instance. Special configuration can be utilized to influence path selection.
Cisco CCNP ROUTE Documenting EIGRP
The implementation of EIGRP should be documented which will be key in troubleshooting. Make sure to keep the documentation current by updating it when changes are made to the network.
Cisco CCNP ROUTE Configuring EIGRP for IP
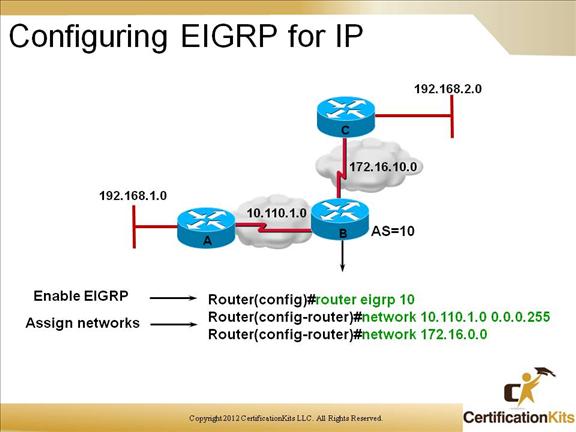
The only funky thing that you have to do is configure the Autonomous Systems that EIGRP will operate in. An autonomous system is simply a group of networks within the same administrative domain.
In order to configure EIGRP in the above diagram you would follow these steps for the appropriate routers:
RouterA(config)#router eigrp 10
RouterA(config-router)#network 10.0.0.0
RouterA(config-router)#network 192.168.1.0
RouterB(config)#router eigrp 10
RouterB(config-router)#network 10.0.0.0
RouterB(config-router)#network 172.16.0.0
RouterC(config)#router eigrp 10
RouterC(config-router)#network 192.168.2.0
RouterC(config-router)#network 172.16.0.0
Just as we discussed earlier that each router must have the same ‘K’ values enabled in order to become neighbors, they must also belong to the same Autonomous System in order for them to recognize each other as neighbors.
If EIGRP routers do not share the same Autonomous System, then in order for them to share routing information, they must redistribute their routes to each other.
Cisco CCNP ROUTE Using the ip default-network Command with EIGRP
Default routes are defined with the ip default-network command when using EIGRP.
Cisco CCNP ROUTE EIGRP load balancing
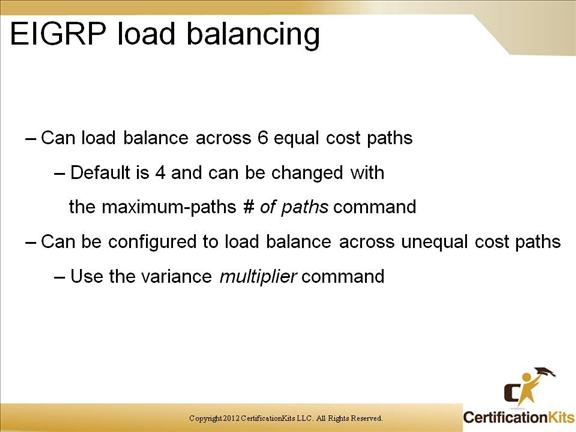
Equal-metric load balancing is the capability of a router to distribute traffic over all its network ports that have the same metric to the destination address. Load balancing increases the use of network segments and increases the effective network bandwidth.
For IP, Cisco IOS Software applies load balancing between a maximum of four equal-metric paths by default. You can configure the maximum number of parallel routes that an IP routing protocol can support using the maximum-paths router configuration command. Up to six equally good routes can be kept in the routing table.
Note: Setting the maximum-paths value to 1 disables load balancing.
When a packet is process-switched, load balancing over equal-metric paths occurs on a per-packet basis. When packets are fast-switched, load balancing over equal-metric paths occurs on a per-destination basis. (Therefore, if you are testing load balancing, do not ping to or from routers with fast-switching interfaces, because the packets that are generated locally by this router are process-switched rather than fast-switched, and the ping might produce confusing results.)
Cisco CCNP ROUTE EIGRP Manual Summarization
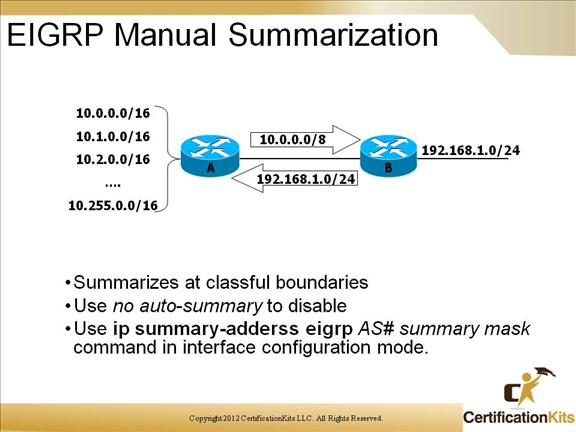
- •Summarizes at classful boundaries
- • To summarize at any subnet or supernet:
(config-if)# ip summary-address eigrp as net mask
- • Inserts a null0 interface entry
- • Typically no auto-summary is also configured – if not then the detailed routes may still appear along with your summary route.
Summarization can also be used to limit the scope of a query for a route that is in the “active” state. If a neighbor fails to reply to query within 3 minutes the route if flagged Stuck in Active and the router resets the neighbor relationship. In some cases, routers that have no way of helping answer a query can cause the route to become SIA – we want to reduce this occurrence.
- • High CPU utilization / overloaded router
- • Low Memory / unable to allocate buffers
- • Intermittent circuit failure
- • Unidirectional traffic flow
Cisco CCNP ROUTE Solutions to Stuck in Active
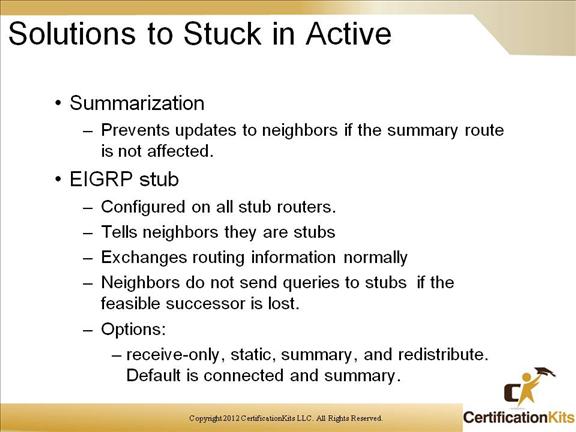
The only additional command that is needed is the eigrp stub command in the stub router configuration.
Router(config)# router eigrp 200
Router(router-config)# eigrp stub
Cisco CCNP ROUTE EIGRP over WAN
While BGP is typically used in the WAN, EIGRP works well in small environments.
Cisco CCNP ROUTE EIGRP Bandwidth Utilization
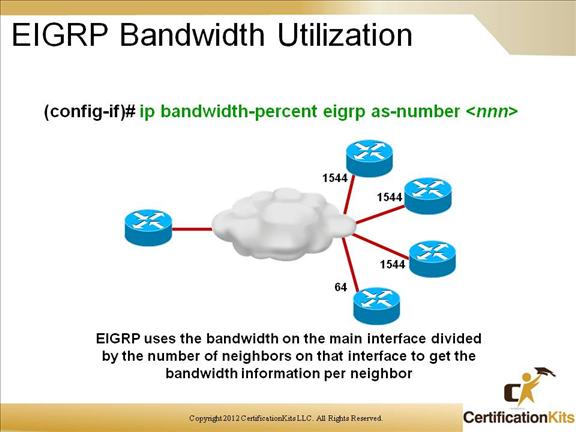
Specifies what percentage of bandwidth EIGRP packets will be able to utilize on this interface
By default, EIGRP uses up to 50% of the link bandwidth. This parameter uses the value specified by the interface’s bandwidth command – usually equal to the CIR. If bandwidth is set artificially low you may need to set this parameter greater than 100. This is used for greater EIGRP load control.
Each PVC might have a different CIR, this might create an EIGRP packet pacing problem. EIGRP uses the bandwidth on the main interface divided by the number of neighbors on that interface to get the bandwidth information per neighbor.
Solution for Multipoint interfaces:
Convert to point-to-point configuration
or
Manually configure bandwidth = (lowest CIR x number of PVCs)
Cisco CCNP ROUTE Router Authentication
Router authentication can be used to validate the source of the routing update prior to adding the information to the routing table. This can prevent attacks that attempt to inject false, potentially malicious routing updates.
Cisco CCNP ROUTE Simple Password vs. MD5 Authentication
There are two types of authentication that Cisco routers support: Simple password and MD5 authentication. The type support is dependant on the routing protocol. MD5 is more secure than simple password.
Cisco CCNP ROUTE MD5 Authentication for EIGRP
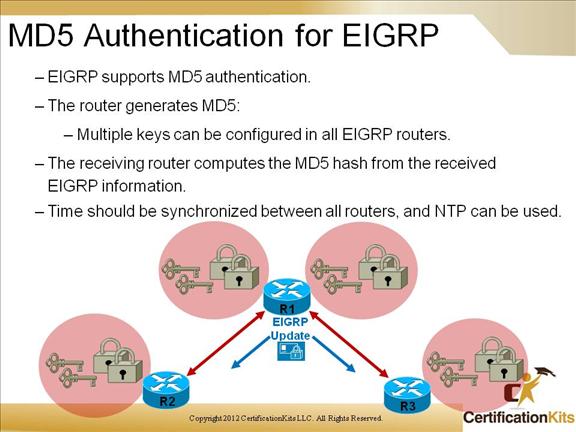
MD5 authentication is supported within EIGRP. As mentioned earlier, it is a good practice to enable MD5 authentication when utilizing EIGRP as a security precaution to thwart off potentially malicious routes from being injected.
Cisco CCNP ROUTE Key Chain
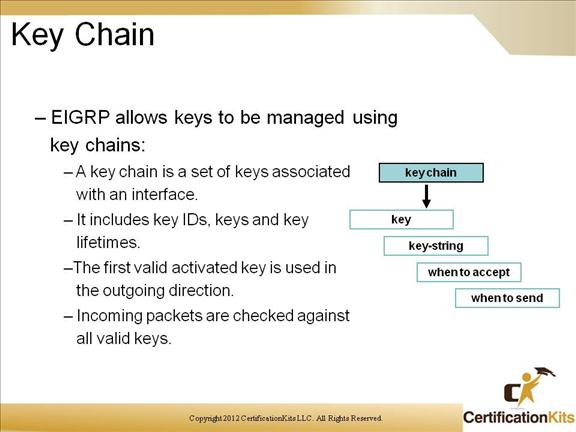
Key chains are used when configuring authentication. Each key within a key chain can specify a “lifetime” which is the time duration the key will be active. IOS examines keys in order from lowest to highest and utilizes the first valid key it finds.
Since keys cannot be utilized when they are not within a valid time, it is critical that for a given key chain, activation times within keys should overlap. Another critical point when implementing is to ensure the router has the correct time synchronize to an external source.
Cisco CCNP ROUTE Planning for EIGRP Authentication
Network requirements must be determined prior to configuring EIGRP authentication. This includes things such as EIGRP autonomous system (AS), EIGRP participating interfaces and participating routers.
Gather all the information and start configuring EIGRP for authentication then verify everything is working properly.
Cisco CCNP ROUTE Configuration for Authentication
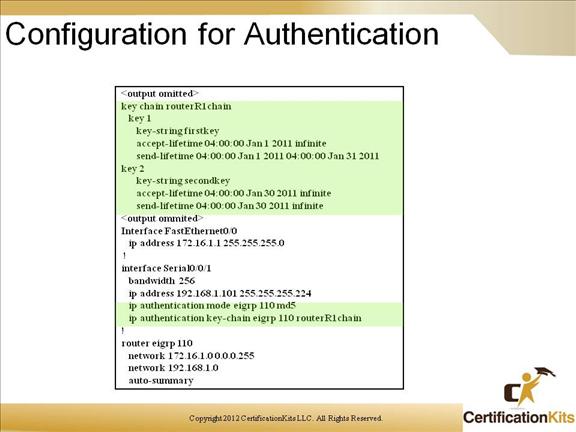
Above is an example of configuring EIGRP to used MD5 authentication. Notice that key chain is configured in global configuration mode while the applying of the authentication is performed under the specific interface, not under router eigrp.
Cisco CCNP ROUTE Debugging EIGRP
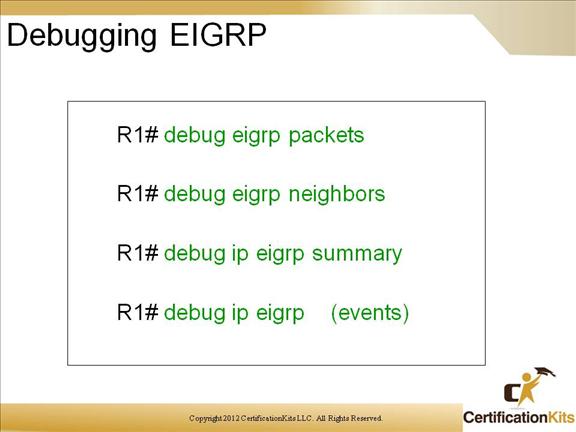
debug eigrp packets – View eigrp packet transmission
debug eigrp neighbors – View eigrp building and maintaining Neighbor tables
debug ip eigrp summary – View summarized eigrp traffic
debug ip eigrp (events) – View all eigrp events
Cisco CCNP ROUTE Monitoring IP EIGRP
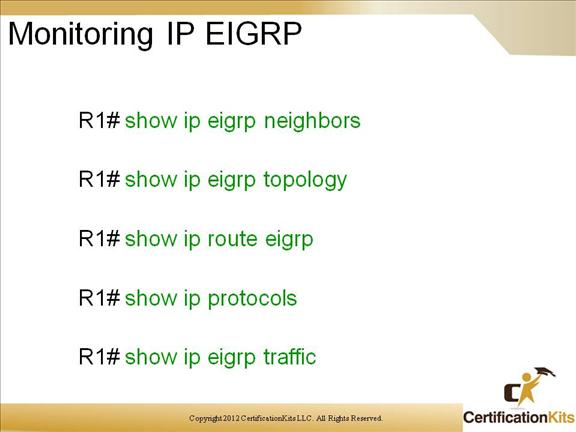
show ip eigrp neighbors – Shows the neighbor table
show ip eigrp topology – Shows the topology table
show ip route eigrp – Shows routes from EIGRP
show ip protocols – Show ip routing protocols configured, the interaction between them as well info about redistribution
show ip eigrp traffic – Shows statistics in reference to hello, updates, queries, replies, and acknowledgements
Cisco CCNP ROUTE Key EIGRP Knowledge
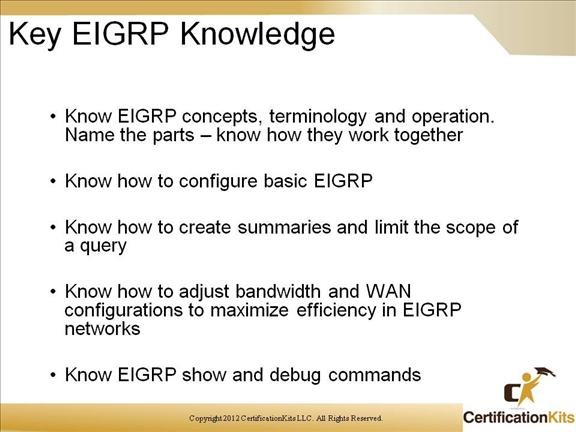
The above slide list key concepts that should be known when learning about EIGRP.
